Tips/Info
It is 2020, and it boggles the mind that there is still a need to train and reinforce the most basic password hygiene practices. However, almost every industry report or study related to data or cybersecurity continues to show an alarming number of users are guilty of disregarding security best practices relating to their passwords.
Treat your passwords like you would your underpants – keep them covered and private.
October is Cybersecurity Awareness Month. Here’s a reminder to keep everything locked up! Anything that your business uses – whether it be computers, applications, software, phones – should be protected to ensure your data is secure. Proper employee training, strong passwords, multi-level authentication, and encryptions are just some of the many ways you can maintain a high level of security.
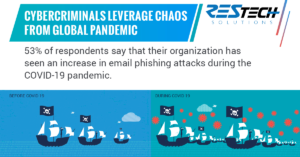
Utilizing fear tactics has been a favorite ploy of cybercriminals for years, but the rise of COVID-19 has brought a significant increase in the amount phishing attacks taking place. The pandemic has given cybercriminals new material to work with, and when combined with their fear tactics, these new approaches are proving to be very successful.
Beware! Cyberthreats come in many forms. Have any of these threats shown up inside your email inbox? Often, these scams will use identity deception to trick or manipulate you by using a fake email from a trusted contact, a sign-up notification from a trusted brand, or a malicious link to a file download. With the right employee training and automated email filters, you can help your business avoid falling prey.
Have you ever received a suspicious email? When in doubt, don’t click! With cybercriminals using email as their preferred method of transporting malware, it is better to delete than take your chances. Better yet, investing in automated phishing defense can help you spot suspicious emails and make the right decision before it’s too late.
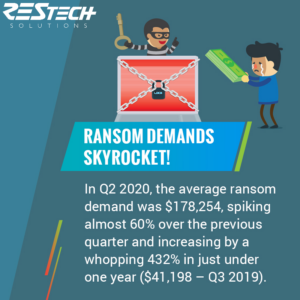
If hit with a ransomware attack, would your business be able to pay off the attacker? As the average cost of a ransom continues to rise, the strength of your data security should also increase. Ask yourself this question: what is your data worth to your business? Would your business continue to run if you lost it all?
Waiting until catastrophe strikes is not the ideal time to determine your business’ cybersecurity initiatives. According to the Ponemon Institute, taking preventative cybersecurity measures before a breach happens can save you up to 82% in the long run, not to mention peace of mind.
With those numbers, what exactly are you waiting for?
A data breach has more underlying costs than just paying a ransom and upping IT security. Reporting a data breach may result in negative consequences that can sometimes be impossible to fix, such as a reduced customer base, lack of trust, and a tarnished reputation. Being hit with a data breach is already catastrophic but rebuilding a reputation can take years.
It would be a mistake to assume that simply because your business data is stored within your cloud applications, that it is secure or that your vendor will have a backup of your data available should you ever need it. In most cases, 3rd party vendors are only responsible for the functionality, performance, and availability. As the customer, it falls solely on your shoulders to ensure your SaaS data is backed up and protected.
Using weak, similar, or duplicate passwords for multiple accounts can leave your business data up for grabs. Securing your defenses with multi-factor authentication, limiting user permissions, and monitoring device usage can greatly reduce your risk of anyone – or anything – getting into your systems.